Data Governance in Microsoft 365: A Framework That Works
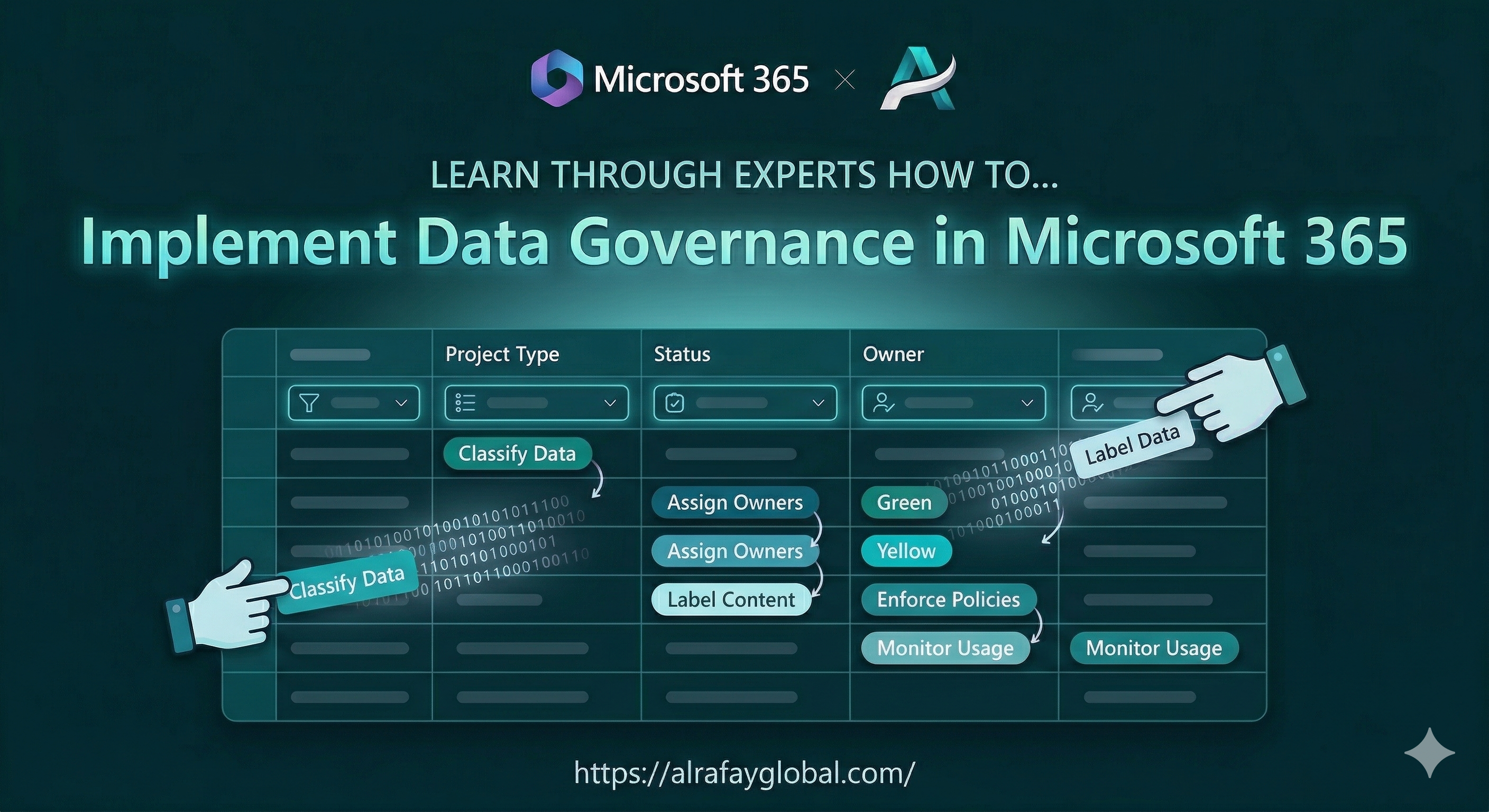
Data Governance in Microsoft 365 is how to implement practical data governance across Microsoft 365 using Purview, sensitivity labels, retention policies, and DLP to protect and manage your data.
How to implement practical data governance across Microsoft 365 using Purview, sensitivity labels, retention policies, and DLP to protect and manage your data.
Al Rafay Consulting
· Updated September 15, 2025 · ARC Team
Why Data Governance Cannot Wait
Every organization running Microsoft 365 is generating data at an accelerating rate. Emails, Teams messages, SharePoint documents, OneDrive files, and Loop pages multiply daily. Without governance, you face:
- Compliance risk — regulated data stored in ungoverned locations
- Security exposure — sensitive documents shared too broadly or accessible to former employees
- Copilot risk — AI tools surface everything a user has access to, making oversharing visible and dangerous
- Storage waste — obsolete data retained indefinitely, inflating costs and complicating eDiscovery
Data governance in Microsoft 365 is not about locking things down — it is about knowing what data you have, where it lives, who can access it, and how long you need to keep it.
The Four Pillars of Microsoft 365 Governance
1. Discovery and Classification
You cannot govern what you do not understand. Start by discovering and classifying your data:
- Microsoft Purview Data Map scans your Microsoft 365 environment and catalogs data assets
- Sensitive information types (SITs) automatically detect patterns like credit card numbers, Social Security numbers, and medical record numbers
- Trainable classifiers use machine learning to identify document categories specific to your organization — contracts, financial statements, HR records
- Content explorer shows you exactly where sensitive data lives across Exchange, SharePoint, OneDrive, and Teams
Run a discovery assessment before implementing any policies. Understanding your current state prevents overly restrictive policies that frustrate users.
2. Protection with Sensitivity Labels
Sensitivity labels classify and protect documents and emails based on their content:
- Label taxonomy — define 3-5 labels that match your organization’s confidentiality levels (Public, Internal, Confidential, Highly Confidential)
- Encryption — Highly Confidential labels can encrypt documents so only authorized users can open them, even if the file is shared externally
- Visual markings — headers, footers, and watermarks that indicate classification level
- Auto-labeling — policies that automatically apply labels based on sensitive content detection (e.g., any document containing more than 10 credit card numbers gets labeled “Confidential”)
- Default labels — set a default label on SharePoint libraries so every new document starts with baseline protection
Sensitivity labels travel with the document. Whether it is downloaded, emailed, or copied to a USB drive, the protection persists.
3. Retention and Lifecycle Management
Not all data should be kept forever. Retention policies ensure data is kept as long as required and deleted when it is no longer needed:
- Retention policies apply broadly to entire locations (all Exchange mailboxes, all SharePoint sites)
- Retention labels apply to specific content based on type, sensitivity, or metadata
- Regulatory records — label content as a regulatory record to prevent modification or deletion during the retention period
- Disposition reviews — require human approval before content is permanently deleted at the end of its retention period
- Adaptive scopes — dynamically target retention policies to specific users, groups, or sites based on Azure AD attributes
A practical retention schedule might look like:
- Emails — retain for 3 years, then delete
- Contracts — retain for 7 years after expiration
- Financial records — retain for 10 years
- Project documents — retain for 2 years after project closure
- Teams chat messages — retain for 1 year
4. Data Loss Prevention (DLP)
DLP policies prevent sensitive data from leaving your organization through unauthorized channels:
- Email DLP — block or warn when users attempt to email documents containing sensitive information to external recipients
- SharePoint and OneDrive DLP — detect sensitive content in files and restrict sharing
- Teams DLP — scan chat messages and shared files for sensitive content
- Endpoint DLP — prevent users from copying sensitive files to USB drives, printing them, or uploading them to unauthorized cloud services
DLP policies should start in test mode (audit only) to understand the volume and nature of detections before enforcing blocks.
Implementation Roadmap
Month 1: Assess and Plan
- Run content explorer and activity explorer to understand your data landscape
- Identify regulatory requirements and map them to Microsoft 365 capabilities
- Define your sensitivity label taxonomy and retention schedule
- Get executive sponsorship — governance requires organizational commitment
Month 2: Pilot
- Deploy sensitivity labels to a pilot group of 50-100 users
- Enable auto-labeling policies in simulation mode to measure accuracy
- Create DLP policies in test mode to observe detection patterns
- Configure retention policies on non-critical content first
Month 3: Expand and Enforce
- Roll out sensitivity labels to all users with training
- Enable DLP enforcement with user-friendly policy tips that explain why an action was blocked
- Apply retention policies to production content
- Establish a governance committee to review incidents and adjust policies
Ongoing
- Review DLP incidents monthly and tune policies to reduce false positives
- Audit sensitivity label usage and address teams that are not labeling content
- Update retention schedules as regulations change
- Reassess quarterly as new Microsoft 365 features become available
Common Mistakes
- Too many labels — users will not choose correctly from a list of 15 sensitivity levels; keep it to 3-5
- Enforcement without training — blocking actions without explaining why creates resentment and shadow IT
- Ignoring Teams governance — Teams is where most collaboration happens; it cannot be exempt from governance
- Set and forget — governance policies need ongoing tuning as your data landscape evolves
Get Expert Help
Al Rafay Consulting implements data governance frameworks across Microsoft 365, from initial assessment through policy enforcement and user training. We help you protect sensitive data without slowing down your business.

Al Rafay Consulting
ARC Team
AI-powered Microsoft Solutions Partner delivering enterprise solutions on Azure, SharePoint, and Microsoft 365.
LinkedIn Profile